The ISC2 Certified Secure Software Lifecycle Professional (CSSLP) certification validates expertise in embedding security practices throughout the entire software development lifecycle (SDLC). This credential signifies a professional's capability to integrate robust security principles from initial requirements gathering to deployment, operations, and maintenance. Earning the CSSLP demonstrates a profound commitment to secure software practices, making it an invaluable asset for developers, architects, and security professionals involved in software creation. This comprehensive guide explores common missteps candidates encounter during their CSSLP journey, offering actionable strategies to navigate and overcome these challenges effectively, ensuring a smoother path to certification.
Navigating the ISC2 CSSLP Examination
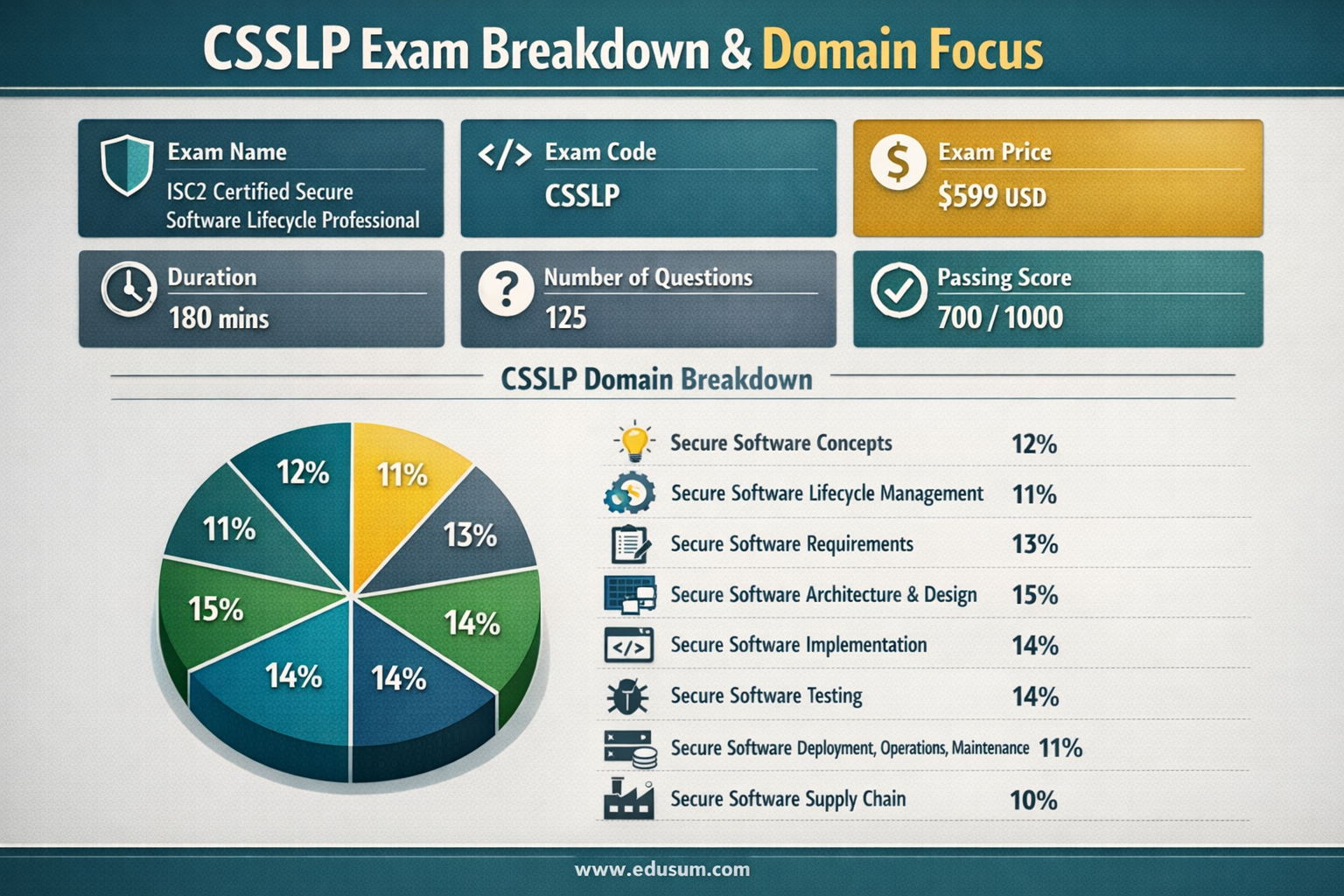
Achieving the ISC2 CSSLP certification requires passing a rigorous examination designed to test a candidate's comprehensive understanding of secure software development. The exam, identified by code CSSLP, is a critical assessment for professionals seeking to demonstrate their proficiency. Successful candidates showcase their ability to apply security best practices across various stages of the SDLC.
The examination details are structured to thoroughly evaluate a candidate's secure software expertise. Understanding these specifics is the first step in formulating an effective study plan and managing expectations for the test day.
Exam Name: ISC2 Certified Secure Software Lifecycle Professional (CSSLP)
Exam Code: CSSLP
Exam Price: $599 (USD). This fee covers the cost of taking the certification examination.
Duration: 180 minutes. Candidates are allocated three hours to complete the entire exam.
Number of Questions: 125. The exam comprises a total of 125 items.
Passing Score: 700 out of 1000. To successfully pass, candidates must achieve a minimum scaled score of 700 points.
These parameters highlight the demanding nature of the CSSLP exam. The 125 questions within a 180-minute timeframe underscore the need for efficient time management and a solid grasp of the subject matter to answer each question accurately and promptly. The specific passing score of 700/1000 further emphasizes the depth of knowledge required across all domains.
Understanding the Core ISC2 CSSLP Syllabus Topics
The ISC2 CSSLP examination is meticulously structured across eight distinct domains, each representing a crucial aspect of the secure software lifecycle. A thorough understanding of these syllabus topics is paramount for any candidate aspiring to excel in the exam. Each domain carries a specific weightage, indicating its relative importance within the overall assessment. Candidates must allocate their study time proportionally to master each area.
The domains and their respective weightages are:
Secure Software Concepts - 12%: This domain lays the foundational understanding of core security principles, encompassing confidentiality, integrity, availability, authentication, authorization, and accountability. It also delves into common attack vectors, security models, and cryptographic concepts. Candidates must grasp how these fundamental ideas underpin all secure software development efforts.
Secure Software Lifecycle Management - 11%: Focuses on integrating security activities into every phase of the software development lifecycle. This includes understanding security roles and responsibilities, defining security policies, and establishing security-related metrics. It emphasizes that security is not an afterthought but an integral part of project management from inception.
Secure Software Requirements - 13%: Addresses the critical process of identifying, documenting, and analyzing security requirements. It covers threat modeling techniques, misuse cases, and privacy requirements. This domain ensures that security is considered at the earliest stages of software design, leading to more resilient applications.
Secure Software Architecture and Design - 15%: This is one of the more heavily weighted domains, focusing on designing secure software architectures and components. It includes topics like secure design principles (e.g., least privilege, defense in depth), security patterns, and secure component design. Architectural decisions made here profoundly impact the software's overall security posture.
Secure Software Implementation - 14%: Concentrates on the actual coding phase, emphasizing secure coding best practices, defensive coding, and identifying and mitigating common vulnerabilities. This domain covers input validation, error handling, session management, and the use of secure development tools and languages.
Secure Software Testing - 14%: Highlights the importance of integrating security testing into the quality assurance process. It includes various testing methodologies such as static application security testing (SAST), dynamic application security testing (DAST), penetration testing, and fuzz testing. Effective testing identifies weaknesses before deployment.
Secure Software Deployment, Operations, Maintenance - 11%: Covers security considerations post-development, including secure deployment strategies, operational security best practices, and ongoing maintenance. Topics include configuration management, incident response, patching, and decommissioning. This ensures security is maintained throughout the software's operational lifespan.
Secure Software Supply Chain - 10%: A more recent but increasingly vital domain, it addresses the security risks associated with third-party components, open-source software, and external dependencies. This includes vendor risk management, software composition analysis (SCA), and ensuring the integrity of the software supply chain.
These domains collectively form the backbone of the CSSLP certification, demanding a holistic and integrated understanding of secure software development. Each area builds upon the others, reinforcing the principle that security must be woven into every thread of the software lifecycle.
Misjudging the SDLC Phases' Security Integration
A common pitfall for many ISC2 CSSLP candidates is underestimating the depth required to understand how security integrates into every phase of the Software Development Lifecycle (SDLC). The exam doesn't merely ask for definitions of SDLC stages; it demands an intricate knowledge of specific security activities, controls, and considerations pertinent to each stage. Simply knowing the names of the phases (requirements, design, implementation, testing, deployment, maintenance) is insufficient; candidates must comprehend the unique security challenges and solutions embedded within each. This holistic view is fundamental to the CSSLP philosophy.
Overlooking Early-Stage Security Requirements
Candidates frequently trip by not sufficiently focusing on the security activities critical during the initial phases of the SDLC.
Inadequate Threat Modeling and Risk Assessment
Many aspiring CSSLPs understand threat modeling conceptually but fail to grasp its practical application and critical importance in the requirements and design phases. They might view it as an optional step rather than a mandatory, iterative process. The exam expects candidates to identify potential threats, analyze vulnerabilities, and propose suitable countermeasures before any code is written. A common mistake is not performing threat modeling rigorously enough, leading to security issues being discovered much later when they are significantly more expensive and complex to fix. This includes overlooking data flow diagrams, trust boundaries, and asset identification as integral parts of the threat modeling process. Without a solid understanding of these initial steps, subsequent security measures may be misaligned or incomplete.
Neglecting Secure Requirement Elicitation
Another significant oversight is a weak understanding of how to effectively elicit and document security requirements. Candidates might focus on functional requirements and treat security as a non-functional afterthought. The CSSLP exam emphasizes that security requirements must be explicitly stated, measurable, and integrated with functional requirements. Failure to define clear security objectives, privacy requirements, and compliance mandates during this phase inevitably leads to software with inherent weaknesses. This includes not knowing how to translate high-level security policies into concrete, testable requirements, which is crucial for building security in from the start.
Underestimating Secure Architecture and Design Principles
The architectural phase is where major security decisions are solidified, making it a high-impact area for potential pitfalls.
Failing to Apply Secure Design Patterns
A frequent mistake is a superficial understanding of secure design patterns. Candidates may know common patterns like MVC or Layered Architecture but struggle with integrating security-specific patterns such as "Security Policy Enforcement Point" or "Single Access Point." The exam tests the ability to select and implement appropriate design patterns that enhance security, reduce attack surfaces, and enforce principles like least privilege and separation of duties. Misapplying or entirely omitting these patterns can introduce systemic vulnerabilities into the software's core structure, creating difficult-to-patch weaknesses.
Ignoring Architectural Risk Analysis
Many candidates do not delve deep enough into architectural risk analysis, which involves evaluating the security implications of architectural choices. This includes understanding the trade-offs between security, performance, and usability at the architectural level. Failing to perform this analysis can lead to designs that are inherently insecure, difficult to audit, or expensive to secure post-hoc. The CSSLP requires not just identification of risks but also proposing architectural solutions that proactively mitigate them. This extends to understanding secure coding best practices such as defensive coding, proper input validation, and secure handling of sensitive data.
Insufficient Domain Depth and Breadth in Study
The ISC2 CSSLP certification spans eight broad domains, each demanding a nuanced understanding. A critical pitfall is a superficial study approach that covers the breadth of topics without delving into the necessary depth, or conversely, focusing too narrowly on familiar areas while neglecting others. The exam questions are designed to test both general knowledge and the application of specific concepts across diverse scenarios. Candidates must strive for a balanced and comprehensive study plan.
Shallow Grasp of Secure Software Concepts
Many candidates falter in the foundational "Secure Software Concepts" domain by not fully internalizing core security principles beyond their definitions.
Confusing Cryptographic Principles and Their Application
A common error is understanding what cryptography is but struggling with when and how to apply specific cryptographic primitives effectively. Candidates might memorize algorithms (e.g., AES, RSA) but fail to grasp their appropriate use cases, key management principles, and potential weaknesses. The exam requires an understanding of symmetric vs. asymmetric encryption, hashing, digital signatures, and Public Key Infrastructure (PKI) in the context of secure software communication and data protection. Incorrect application of cryptographic concepts can lead to false senses of security or introduce new vulnerabilities.
Misinterpreting Security Models and Access Controls
Another area of weakness is a shallow understanding of security models like Bell-LaPadula, Biba, and Brewer-Nash (Chinese Wall), or access control mechanisms such as Role-Based Access Control (RBAC), Discretionary Access Control (DAC), and Mandatory Access Control (MAC). Candidates might know the names but struggle with their underlying principles, differences, and suitability for various software environments. The CSSLP requires not only recognizing these models but also identifying their strengths, limitations, and how they enforce security policies within an application. An inability to discern the appropriate access control model for a given scenario is a significant hurdle.
Overlooking Secure Software Supply Chain Complexities
The "Secure Software Supply Chain" domain, while having a lower weightage (10%), is increasingly complex and often overlooked by candidates focusing on more traditional SDLC phases.
Ignoring Third-Party Component Vulnerabilities
Many candidates fail to appreciate the profound security implications of using third-party libraries, open-source components, and external APIs. They might concentrate solely on the code they write, assuming external components are inherently secure. The CSSLP emphasizes the need for Software Composition Analysis (SCA) tools, vulnerability scanning of third-party dependencies, and understanding licenses. A pitfall is not recognizing that a single vulnerable library can compromise an entire application, making supply chain security a critical area of focus.
Inadequate Vendor Risk Management
Another challenge lies in understanding the principles of vendor risk management within the software supply chain. Candidates may not fully grasp the processes for evaluating external software providers, assessing their security postures, and integrating contractual security requirements. The exam expects knowledge of due diligence, auditing third-party code, and managing the risks associated with outsourcing software development or using externally hosted services. This domain extends beyond technical scanning to encompass governance and procurement practices vital for overall software integrity.
Over-reliance on Memorization, Neglecting Application
The ISC2 CSSLP exam is not merely a test of recall; it's an assessment of a candidate's ability to apply secure software principles to real-world scenarios. A significant pitfall is an over-reliance on rote memorization of terms, definitions, and concepts without a deeper understanding of their practical application. This approach often leads to difficulties when confronted with scenario-based questions that require critical thinking and problem-solving.
Failing to Understand "Why" and "How"
Candidates who only memorize often struggle when questions ask for the rationale behind a security measure or the steps to implement a secure design.
Surface-Level Knowledge of Secure Software Implementation
In the "Secure Software Implementation" domain, for instance, a candidate might memorize a list of secure coding best practices (e.g., input validation, parameterized queries). However, they might lack the deeper understanding of why input validation is crucial (preventing injection attacks) or how to properly implement it across various data types and input sources. The exam will present code snippets or design problems and ask candidates to identify vulnerabilities or suggest secure alternatives, tasks that pure memorization cannot address. Understanding the underlying attack vectors and mitigation techniques is far more valuable.
Lack of Contextual Understanding for Secure Testing
Similarly, in "Secure Software Testing," a candidate might memorize different testing types (SAST, DAST, penetration testing). Yet, without understanding the context when to apply each method, what vulnerabilities each is best suited to find, and how to interpret their results they will falter. The exam requires candidates to choose the most appropriate testing strategy for a given software scenario or to analyze test results to recommend corrective actions. This requires more than definitions; it demands a functional understanding of testing's role within the SDLC. A key resource for practice and understanding different question types can be found through platforms offering CSSLP exam sample questions.
Skipping Practical Exercises and Case Studies
To combat the memorization trap, active engagement with practical scenarios is crucial.
Ignoring Scenario-Based Problem Solving
Many candidates skip working through scenario-based problems or case studies, preferring to stick to theoretical reviews. The CSSLP exam heavily features such questions, requiring candidates to act as secure software professionals, making decisions based on limited information and applying multiple security principles. Without practicing these types of problems, candidates often struggle with synthesis and analytical thinking under exam conditions. This includes identifying trade-offs and selecting optimal solutions in complex situations, a skill that pure memorization does not foster.
Limited Exposure to Real-World Vulnerabilities
A pitfall is studying security vulnerabilities in isolation, without understanding their real-world impact or how they manifest in actual software. For example, a candidate might know about SQL Injection but not understand how various sanitization techniques work or the broader implications of data compromise. Engaging with common vulnerability examples, like those found in OWASP Top 10, and analyzing their remediation strategies is vital. This provides the practical context needed to connect theoretical knowledge to applied security solutions, which is what the CSSLP aims to certify.
Inadequate Practice and Poor Time Management
The ISC2 CSSLP exam is a lengthy and demanding assessment, requiring both extensive knowledge and the ability to manage time effectively under pressure. A common pitfall for candidates is inadequate practice, particularly with full-length mock exams, leading to poor time management during the actual test. This can result in rushed answers, missed questions, and unnecessary stress, even for those with a strong theoretical understanding.
Neglecting Simulated Exam Environments
Candidates often underestimate the importance of simulating the actual exam experience, leading to performance issues on test day.
Insufficient Practice with Exam Timings
Many individuals study diligently but fail to take practice tests under timed conditions. They might review questions at their leisure, not realizing the pace required for 125 questions in 180 minutes. This translates to approximately 1 minute and 26 seconds per question. Without practicing within this constraint, candidates can easily fall behind, forcing them to guess or skip questions towards the end. Regular, timed practice helps develop a natural rhythm and improves decision-making speed. This also helps in identifying areas where one spends too much time, allowing for targeted improvement.
Ignoring Full-Length Mock Exams
A critical mistake is not taking enough full-length mock exams. These simulations are invaluable for building stamina, reducing test anxiety, and identifying weaknesses in both knowledge and exam-taking strategy. Short quizzes or domain-specific practice questions are helpful, but they don't prepare candidates for the mental endurance required for a three-hour exam. Ignoring this aspect often leaves candidates unprepared for the psychological and physical demands of the actual test.
Poor Strategy for Question Analysis and Response
Beyond mere timing, candidates often lack a refined strategy for approaching different question types.
Rushing Through Complex Questions
The CSSLP exam includes scenario-based and multi-faceted questions that require careful reading and analysis. A pitfall is rushing through these complex items, misunderstanding the core problem, or missing critical details embedded in the question stem. Effective time management involves knowing when to spend more time on a challenging question and when to flag it for review, rather than getting stuck. Developing a strategy to break down complex questions into manageable parts can save valuable time and improve accuracy.
Ineffective Use of Flagging and Review Techniques
Many candidates do not effectively utilize the exam interface's flagging feature. This leads to them either dwelling too long on difficult questions or not having enough time to revisit them. A smart strategy involves making an educated first pass, flagging uncertain questions, and then returning to them if time permits. Without this discipline, candidates can get bogged down, jeopardizing their overall score. Practicing this technique during mock exams is essential to ensure it becomes second nature on the actual test.
Ignoring the ISC2 Mindset and Ethical Preparation
The ISC2 CSSLP certification, like all (ISC2) credentials, emphasizes a specific professional mindset and strict ethical conduct. A significant pitfall for candidates is ignoring this inherent philosophy, which permeates the exam content and the expectations of a certified professional. Furthermore, engaging in unethical preparation methods, such as using "exam dumps," not only jeopardizes one's certification but also undermines the integrity of the profession.
Misunderstanding the (ISC2) Code of Ethics
The (ISC2) Code of Ethics is not just a formality; it guides the entire secure software lifecycle professional's conduct.
Failing to Integrate Ethical Principles
Candidates sometimes view the Code of Ethics as separate from the technical domains. However, questions on the CSSLP exam often subtly test ethical considerations in decision-making, especially in scenarios involving data privacy, intellectual property, and responsible disclosure of vulnerabilities. Failing to integrate these ethical principles into one's problem-solving approach can lead to incorrect answers, as the "most secure" technical solution may not always be the "most ethical" or appropriate one. Understanding how security decisions impact various stakeholders is critical.
Neglecting Professional Responsibility in Scenarios
The exam frequently presents scenarios where a CSSLP professional must balance security imperatives with business needs, legal compliance, and ethical duties. A pitfall is focusing purely on technical aspects without considering the broader professional responsibilities. For instance, questions might involve situations where a discovered vulnerability could be exploited, and the candidate must choose a response that aligns with responsible disclosure and minimizing harm, not just technical patching. This holistic view of professional duty is a cornerstone of (ISC2) certifications.
Engaging in Unethical Study Practices
The allure of shortcuts can lead candidates down a perilous path that compromises the value of their certification.
Over-reliance on Exam Dumps
A grave and detrimental pitfall is using "exam dumps" as a primary study method. These materials, often illegally sourced or compiled from memory, contain actual exam questions or close approximations. While they may seem like an easy way to pass, they violate the (ISC2) Code of Ethics and often lead to superficial learning. Candidates who rely on dumps typically lack the foundational understanding required to perform effectively in a real-world secure software role, and if discovered, can lead to permanent disqualification from all (ISC2) certifications.
Misinterpreting Practice Question Intent
Even when using legitimate practice questions, some candidates treat them as a means to memorize answers rather than to understand concepts. The purpose of practice questions is to test comprehension, identify weak areas, and familiarize oneself with the exam format. A pitfall is simply memorizing the correct answer for a given question without understanding the why behind it. This approach fails when the actual exam presents the same concept in a slightly different scenario or wording, exposing the lack of true knowledge. Ethical and effective preparation involves using official training resources and reputable study guides.
Underestimating Exam Structure and Question Nuances
The ISC2 CSSLP exam is known for its intricate question phrasing and the need for a precise understanding of the most appropriate answer among several plausible options. Many candidates trip by underestimating these nuances, leading to misinterpretations and incorrect selections, even when they possess a good general knowledge of the subject matter. The structure of the questions and the subtle distinctions in answer choices are designed to truly test a candidate's mastery, not just their familiarity.
Challenges with Multiple-Choice Question Design
The multiple-choice format, while seemingly straightforward, holds specific traps for the unprepared candidate.
Identifying the "BEST" Answer, Not Just a "CORRECT" One
A pervasive pitfall is failing to distinguish between a merely correct answer and the best answer in a given context. CSSLP questions often present multiple options that are technically correct, but only one option most comprehensively or appropriately addresses the scenario presented, often aligning with (ISC2) best practices. Candidates must train themselves to critically analyze each option, consider the broader implications, and select the response that offers the most robust, ethical, or complete solution within the secure SDLC framework. This requires a deep understanding of priorities and trade-offs.
Decoding Complex Scenario-Based Questions
The exam frequently uses lengthy, scenario-based questions that describe a specific situation, challenge, or problem within a software development context. A common mistake is getting lost in the narrative or misidentifying the core problem the question is asking to solve. Candidates must develop the skill of rapidly extracting key information, identifying the relevant security domain, and filtering out extraneous details. Without this ability, even well-prepared individuals can struggle to correctly interpret the question's intent and select the appropriate answer.
Misinterpreting Keywords and Contextual Cues
Subtle wording in questions and answer choices can significantly alter their meaning and lead to errors.
Overlooking Specific Quantifiers and Modifiers
Questions often include subtle quantifiers (e.g., "always," "never," "most likely," "least likely") or modifiers that significantly change the meaning of a statement. A pitfall is a superficial reading that glosses over these critical words, leading to an incorrect interpretation of the question's scope or expected outcome. Candidates must pay meticulous attention to every word in both the question and the answer options to ensure their chosen response accurately reflects the specific conditions laid out. This demands careful, deliberate reading rather than skimming.
Struggling with Terminology and Jargon
While a strong vocabulary in secure software development is essential, candidates sometimes struggle with subtle distinctions in terminology. The exam may use terms that are similar but have different implications in specific contexts, or it might use jargon in a way that requires a precise understanding. A pitfall is conflating related concepts or misinterpreting the precise meaning of a technical term, which can lead to selecting an incorrect answer. Continuous review of definitions and their practical applications, as well as understanding the terminology used in official training is vital for overcoming this.
Remedying Knowledge Gaps with Structured Study
Identifying and systematically addressing knowledge gaps is crucial for CSSLP candidates. A common pitfall is a haphazard study approach that does not effectively target weak areas, leading to repeated errors and a lack of confidence. A structured study plan, combined with targeted remediation, is essential to ensure comprehensive coverage of all domains and to reinforce understanding where it is most needed. This strategic approach transforms weaknesses into strengths.
Systematic Weakness Identification
Effective study begins with an honest assessment of current knowledge and areas requiring improvement.
Skipping Detailed Review of Incorrect Answers
A significant mistake candidates make is simply noting a question as "wrong" without delving into why it was incorrect. The real learning occurs in the detailed analysis of wrong answers. Was it a conceptual misunderstanding? A misinterpretation of the question? A lack of knowledge in a specific sub-domain? A pitfall is failing to use incorrect answers as diagnostic tools to pinpoint precise knowledge gaps. Each wrong answer is an opportunity to learn, reinforce understanding, and prevent future errors.
Neglecting Cross-Domain Interdependencies
The CSSLP domains are highly interconnected. A weakness in "Secure Software Concepts" can manifest as difficulties in "Secure Software Architecture and Design." A pitfall is addressing domains in isolation without understanding how they influence and depend on each other. Remediation should involve not only strengthening knowledge within a specific domain but also understanding its relationships with others, recognizing that security is a holistic endeavor. This integrated view is what the CSSLP exam truly assesses, requiring candidates to connect the dots across the entire lifecycle.
Targeted Study and Resource Utilization
Once weaknesses are identified, focused efforts are required to close those gaps.
Ineffective Use of Official Study Resources
Many candidates either underutilize or misuse official study guides and training materials provided by ISC2 or authorized partners. A pitfall is relying solely on third-party resources that may not align perfectly with the exam's focus or depth. Official materials provide the most accurate and authoritative interpretation of the exam objectives. Candidates should treat these resources as their primary source of truth, complementing them with other high-quality materials rather than substituting them. This ensures alignment with the exam's essential secure lifecycle concepts.
Lack of Diverse Learning Modalities
Some candidates stick to a single study method, such as reading a book, even if it's not effective for their learning style. A pitfall is failing to incorporate diverse learning modalities, such as video lectures, hands-on labs (if applicable), flashcards, and group discussions. Different formats can explain complex concepts in new ways, reinforcing understanding. For instance, visually explaining an attack vector might be more effective than reading about it. Adopting a multi-modal approach helps solidify knowledge from various angles and caters to different cognitive preferences.
Sustaining Momentum and Mental Well-being
The journey to ISC2 CSSLP certification is a marathon, not a sprint. A frequent pitfall for candidates is failing to maintain consistent study momentum and neglecting their mental and physical well-being throughout the rigorous preparation period. This can lead to burnout, decreased retention, and reduced performance on exam day, regardless of prior knowledge. Sustaining focus requires a balanced approach that integrates study with self-care.
Combating Burnout and Mental Fatigue
Extended periods of intense study without breaks can be counterproductive, leading to diminishing returns.
Ignoring the Need for Regular Breaks
Candidates often push themselves through long, uninterrupted study sessions, believing that more hours equate to better preparation. However, this often leads to mental fatigue, reduced concentration, and poor information retention. A pitfall is failing to incorporate regular, short breaks (e.g., 10-15 minutes every hour) and longer breaks (e.g., a full day off each week) into their study schedule. These breaks are crucial for cognitive rest, consolidation of learned material, and preventing burnout. They allow the brain to reset and return to study sessions with renewed focus.
Neglecting Physical Health and Sleep
The impact of physical health on mental performance is often overlooked. A common mistake is sacrificing adequate sleep, nutrition, and exercise for more study time. Lack of sleep impairs cognitive functions, memory, and critical thinking all vital for the CSSLP exam. Poor nutrition and a sedentary lifestyle can further exacerbate fatigue and stress. A pitfall is treating physical well-being as secondary, which can significantly undermine intellectual capacity and overall exam performance. Prioritizing health is an investment in successful preparation.
Maintaining Motivation and Discipline
The long study period can test one's resolve, making consistent motivation challenging.
Studying in Isolation without Peer Support
Many candidates choose to study entirely in isolation, which can lead to feelings of overwhelm and demotivation when encountering difficult topics. A pitfall is failing to connect with peer groups, study buddies, or online forums dedicated to CSSLP preparation. These communities offer opportunities to discuss challenging concepts, share insights, provide mutual encouragement, and break the monotony of solitary study. Explaining concepts to others or asking for clarification can deepen understanding and keep motivation levels high.
Losing Sight of the End Goal and Benefits
During arduous study periods, it's easy to get bogged down in the details and lose sight of why one started this journey. A pitfall is failing to regularly revisit and reaffirm the career and professional benefits of achieving the ISC2 CSSLP certification. Reminding oneself of the enhanced job opportunities, increased earning potential, and validation of expertise can serve as a powerful motivator to push through challenging phases. Keeping the "big picture" in mind helps maintain perspective and renews commitment, ensuring the candidate remains focused on their ultimate objective.
Optimizing Pre-Exam Preparation and Test Day Execution
The final phase of ISC2 CSSLP preparation involves fine-tuning study efforts and strategically approaching the exam day itself. Many candidates, despite extensive study, trip up in these crucial moments due to last-minute anxieties, poor logistical planning, or ineffective test-taking strategies. Optimizing these final steps can significantly enhance performance and reduce preventable errors.
Last-Minute Preparation Traps
The days leading up to the exam require a careful balance of review and rest.
Cramming New Material Right Before the Exam
A critical and often counterproductive pitfall is attempting to cram large amounts of new material in the final 24-48 hours before the exam. This typically leads to increased anxiety, information overload, and confusion, rather than effective learning. The brain needs time to process and consolidate information. The days before the exam should be dedicated to light review of challenging topics, revisiting summary notes, and getting adequate rest, not introducing entirely new concepts. This allows previously learned material to solidify.
Underestimating the Importance of a Clear Mind
Candidates often neglect the psychological aspect of exam readiness. A pitfall is entering the exam mentally exhausted or overly stressed. A clear, calm mind is essential for critical thinking and analytical reasoning. Ensuring sufficient sleep, a healthy meal, and minimizing external stressors on the day of the exam can make a substantial difference. Techniques such as mindfulness or brief meditation can help manage pre-test jitters, allowing for optimal cognitive function during the three-hour assessment.
Strategic Test Day Execution
Success on exam day is not just about knowledge, but also about execution under pressure.
Poor Management of Exam Time
Even with practice, some candidates struggle with real-time adaptation during the exam. A pitfall is failing to allocate time per question effectively, getting stuck on difficult items, or not pacing oneself. A strategic approach involves quickly assessing question difficulty, making an educated guess if truly stumped, flagging for review, and moving on. The goal is to answer all 125 questions, even if some require a quick decision, rather than leaving many unanswered due to dwelling on a few. This pragmatic approach maximizes the chances of hitting the passing score.
Failing to Read Questions and Answers Carefully
Under exam pressure, candidates might rush through questions and answer choices, leading to misinterpretations. A common pitfall is overlooking subtle keywords, double negatives, or critical context that can change the entire meaning of a question or an answer option. This can lead to selecting an incorrect answer even when the candidate knows the underlying concept. Deliberate, careful reading of every word, twice if necessary, can prevent these easily avoidable errors and ensures the candidate is responding to the exact question asked.
The ISC2 CSSLP certification is a rigorous yet highly rewarding credential for secure software professionals. The journey to passing the exam is fraught with potential pitfalls, from misjudging the depth of required knowledge across SDLC phases to underestimating the exam's structural nuances and neglecting personal well-being. By proactively addressing these common mistakes through structured study, comprehensive domain understanding, ethical preparation, and strategic test-day execution candidates can significantly enhance their chances of success. Embrace a holistic approach to preparation, focusing on true comprehension and application, and you will be well-equipped to avoid these avoidable traps and achieve your CSSLP certification. For continued professional growth and access to more secure software development insights, consider exploring relevant resources and communities.Explore more resources for professional growth and industry insights on cybersecurity learning paths.
Frequently Asked Questions
1. What does the ISC2 CSSLP certification validate?
The ISC2 CSSLP certification validates a professional's expertise in incorporating security practices throughout the entire software development lifecycle (SDLC), from requirements gathering to deployment and maintenance. It demonstrates the ability to proactively secure software at every stage.
2. How long is the ISC2 CSSLP exam and how many questions does it have?
The ISC2 CSSLP exam has a duration of 180 minutes (3 hours) and consists of 125 multiple-choice questions. Candidates need to manage their time efficiently to answer all questions.
3. What is the passing score for the CSSLP exam?
To pass the CSSLP exam, candidates must achieve a scaled score of 700 out of 1000 points. This score reflects a comprehensive understanding of the secure software development domains.
4. Are there any prerequisites for the ISC2 CSSLP certification?
Yes, candidates typically need a minimum of four years of cumulative paid work experience in one or more of the eight CSSLP domains. A one-year experience waiver may be granted for a four-year college degree or an approved certification, but this varies and should be confirmed with ISC2 directly.
5. Why is the secure software supply chain a critical domain for CSSLP?
The secure software supply chain is critical because modern software heavily relies on third-party components and open-source libraries, which can introduce significant vulnerabilities if not properly managed. This domain ensures professionals can assess and mitigate risks associated with external dependencies.



Write a comment ...